List in Translation: An ACI Migration Study…Just for Fun!
I’m super excited to share this article with you! For this one I had the opportunity to team up with, and learn from, my friend, fellow Cisco Champion, and Cisco Learning Network VIP – Micheline Murphy!
Earlier this year I was working with a customer that was transitioning from a traditional Data Center network architecture to Cisco ACI. I was having a really difficult time wrapping my head around translating an ACL to an ACI Contract, so I turned to Micheline for some help – and help me she did!
Design Considerations
We’re working with a customer that is moving to from a traditional three-tier network architecture to Cisco ACI. The customer, we’re going to call them Acme Bowling[ii], is a large global company with many sites and multiple data centers. For this deployment, only the Boston data center is targeted for the migration to ACI.
The Data Center located in Boston MA uses a subnet of 10.100.0.0/16. There are also two other data centers, one on the West Coast of the United States and using a subnet of 10.101.0.0/16 and another in the United Kingdom using a subnet of 10.102.0.0/16.
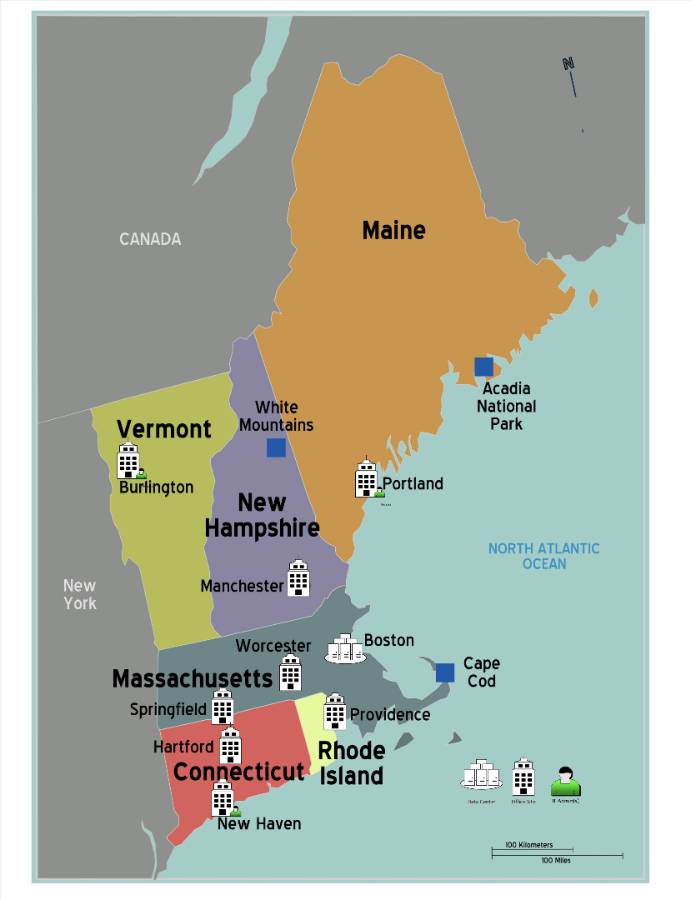
The company has office locations around the world and, depending upon the size of the site, they use a subnet within either the 172.16.0.0/12 or 192.168.0.0/16 RFC 1918 address spaces. The IT administrative team is located mostly within New England. IT administrators sit in Burlington VT, Portland ME, and New Haven CT. The IT admin’s workstations have been assigned static IPs within the subnet for their respective sites. The IT admins are not given special subnets restricted to administrative access. So, there are other clients within these same subnets with differing security permissions.
Customer policy requires that the network blocks access to administrative ports for SSH, HTTPS, and RDP (ports 22, 443, 3329) by end user subnets. However, the IT administrative team is located within these same subnets and must have remote access to these administrative ports. Additionally, the client subnets need to have access to all other ports to gain access to services hosted within the data center.
Here is a list of static IP addresses in use by the IT Administrative team, and the sites at which they are located.
Burlington, VT Portland, ME New Haven, CT
172.19.20.45 172.20.18.15 192.168.32.10
172.19.20.46 172.20.18.20 192.168.32.12
172.19.20.47
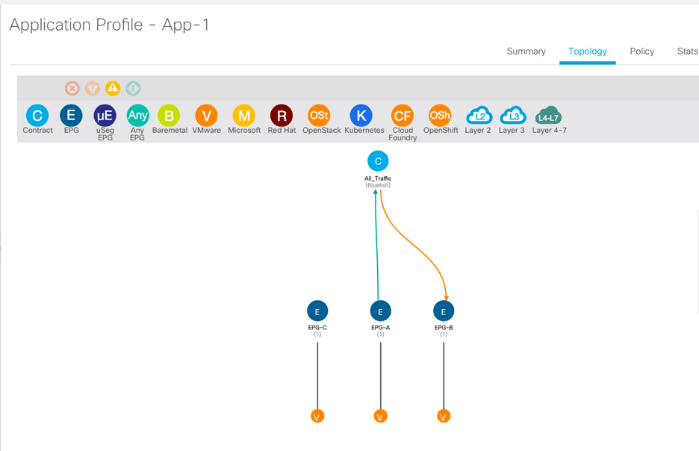
We need ACI to be able to:
- Allow access to administrative ports (SSH, HTTPS, and RDP) from the administrator IPs and the other data centers.
- Block access to administrative ports from all other client subnets.
- Allow access to all other ports from all Client Subnets so they may utilize services hosted at the DC.
To see where we go from here in ACI you can read the rest of the article on the Cisco Learning Network Blog!

One thought