My Thoughts on Networking Field Day 21
Recall a few weeks ago I announced that I was selected to be a delegate for Networking Field Day 21. Well NFD21 has come and gone, and let me tell you – NFD Hangover is real… More about that later.
But, now that NFD21 is over I wanted to share with you my thoughts on the presentations I was apart of.
NFD21 was the largest Networking Field Day event to date! There were 17 delegates, and 13 presenters/sponsors spanning four days. The massive delegate team was broken up into different groups. Some delegates were there for the entire event, others were there just the first two days, and the rest were there for the back half. I was part of the back half of the group and got to see presentations from: Network to Code, DellEMC (networking), Forward Networks, Aruba, Extreme Networks, and Ixia.
I’ll take you through my perspective of each presentation and give some thoughts I what heard and saw.
Network to Code
First up was Network to Code, presenters were Jason Edelman, Damien Garros, Jeremy Stretch, and John Anderson.
The team at Network to Code took us on a Network Automation Journey. We learned who they were, what their mission is, and then they did a great job of going over all the various parts and pieces of Network Automation. They discussed the need for a Source of Truth and not having it always be going straight to the network itself. They touched on ways that humans and the business can interact through tools like Confluence, ServiceNow, Slack, Microsoft Teams, and even Cisco Webex Teams. They even did some really cool demos using Slack illustrating how network engineers could pull data about the network into their running chat using Slack’s chat integrations with other tools. It was very cool!
The journey continued with an overview of their services and what the transition looks like going from traditional network operations and management to Network Automation.
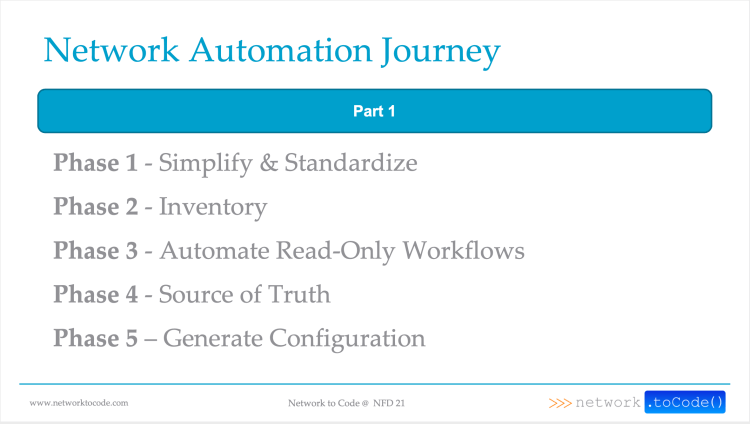
I thoroughly enjoyed the presentation because all the presenters were engaging and the content was very pointed. My key take aways were that if you want to start automating in your network you can’t start with an environment in disarray. It’s hard to automate chaos. Learn to crawl and walk before you start to run and sprint. Start with simple projects like connecting to devices and pulling information from show commands, for example. Don’t dive right in to trying push config.
If you’re interested in starting your network automation journey, and want some help and guidance along the way, make sure you reach out to the team at Network to Code.
Netbox with Jeremy Stretch

After the the Network Automation journey we got to hear about Netbox from the creator himself, Jeremy Stretch. Jeremy spoke to the delegate team about how Netbox came to be and it’s history, it sure has come a long way over the past four years.
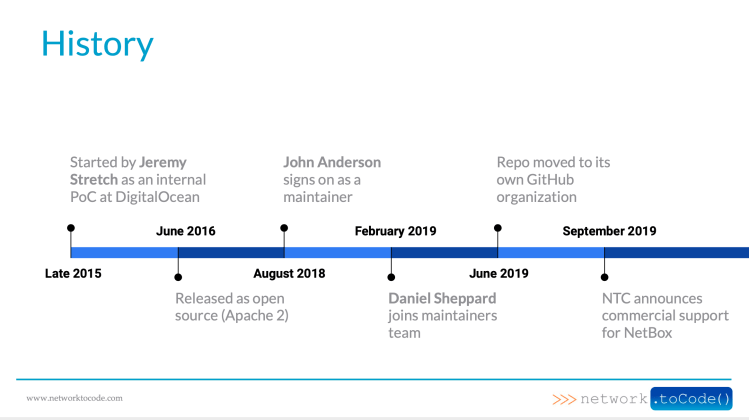
Jeremy’s presentation on Netbox has inspired me to learn more about it and in the future I plan to do some blog posts on setup and configuration of Netbox. I see an awful lot of value that Netbox brings and I believe it’ll be a valuable tool to the people I work with and plan to help spread the word about Netbox.
I can’t forget to tell you about the NetworktoCode Slack Channel. It’s free to join, you just have to request an invite through their web page. The Slack Channel is 10K members strong, and growing. In there people are sharing their experience, asking questions, and the team at NetworktoCode will even invite you to create a channel for projects you’re working on.
DellEMC
The next presentation on my first day was from DellEMC, networking division. Their presentation was two parts, the first on their new Software Defined Networking Data Center solution and the second half covered their new SD-WAN solution.
SmartFabric Director

Now, I’ve been working with Data Center a lot lately and at the first sign of the announcement was initial reaction was that I was excited to see another big player enter into the DC SDN arena.
However, the presentation of the initial release of the product was a bit under whelming, given the source. I expected a little bit more features and a more polished UI experience. That all being said this is just the initial release of SmartFabric Director.
Given the tight relationship between Dell and VMware, SFD will undoubtedly have some unmatched tighter integrations with VMware than it’s competitors. This will be a product to keep an eye on and watch how it evolves.
SD-WAN
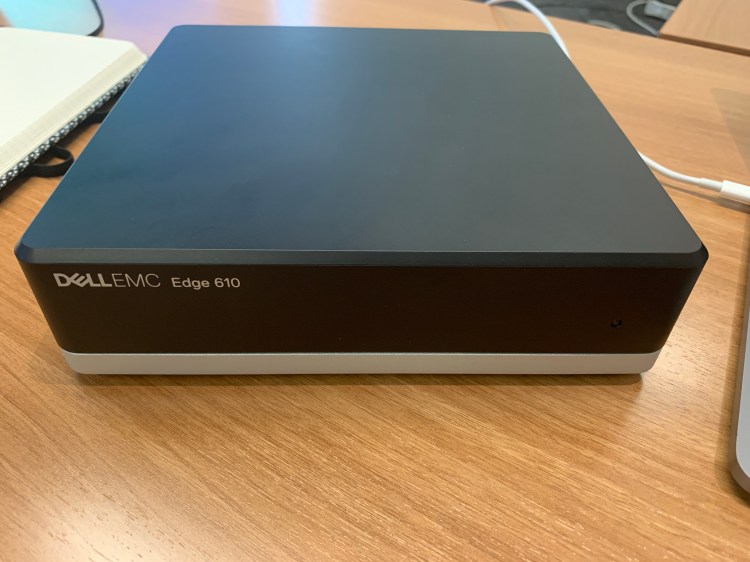
The next part of DellEMC’s presentation was on their new SD-WAN offering. The offering is built on top of VeloCloud, but is a DellEMC branded solution. Nearly two years ago VMware acquired VeloCloud,so it wasn’t a total surprise to see the two combine to make such an offering.
The presentation touted how easy it is deploy the new Edge 610 with the DellEMC hosted Orchestrator. However, out of the gate the solution is lacking critical enterprise features, like IPv6 support of any kind, and ZTP (Zero Touch Provisioning). While it sounded like ZTP would be coming soon it sounded less the case for IPv6 support.
Forward Networks

Let me start off by saying Forward Networks was by far my favorite presentation of NFD21 for me (and no, it wasn’t because they had a Boba tea bar waiting for us at their office). If you haven’t had Boba Tea find some near you and try it – it’s really good!
Beyond the Boba tea is the amazing technology and people behind Forward Networks. Forward Networks can run an entire software copy of your network, what they call a “Digital Twin,” so you can do things like evaluate new ACL rules, test new code, see where traffic is getting blocked, see if your network is ready for that new application the CEO wants straight away – and you can do it all without touching production. You can even query the network to see where certain VLANs exist
The presentation was engaging, the technology was amazing, their process on how they test and built support for all the major Network Operating Systems left me on the edge me seat the whole time we were there. They support OS from Cisco, Juniper, AWS, Arista, and Palo Alto just to name a few. And, they go deeper too. They don’t just know Cisco’s IOS, they work with IOS-XE, XR, and Cisco Nexus.
They even debuted a new feature, called In-App Custom Checks, for us right there during their NFD presentation, They also walked us through some really cool demos like integrations with Slack and Ansible.
And, since NFD21 Forward Networks has recently announced they’ve secured $35M in Series C funding. Well deserved for this team of hard workers! This tool is absolutely game changing to network engineers and operators. If you’re interested in learning more you can get yourself a 90-day free trial. I cannot wait to see what Forward Networks does next!
Aruba

The Aruba NFD21 presentation was another two part presentation that covered the release of their new SD-WAN solution they’re calling SD-Branch, and they dove in deep with the AOS-CX OS.
It started with an introduction from Aruba CTO, Partha Narasimhan, who gave an overview of Aruba, it’s history, as well as an overview of what we could expect to see from them.
Next, we jumped into SD-Branch. Aruba refers to their solution as SD-Branch because it encompasses the SD-WAN and SD-LAN as well. It includes Aruba’s best-in-class WAN, LAN, and Wireless, all controlled from Aruba cloud Orchestrator.
After a solid introduction of SD-Branch we dove in on demos. The demos consisted of deployment and setup, connecting to cloud, and creating policy and VPNs. The UI was extremely clean, and familiar – which then of course makes it easier to navigate.
After SD-Branch we jumped into AOS-CX and the advancements the Aruba team is making. AOS-CX promises to simply network operations. Their new software suite called NetEdit can help maintain config consistency across your entire network. It can also ensure that device configs conform to your organization’s standard.
My take away from the Aruba presentation is that if I were considering either an SD-WAN/LAN solution or upgrading network infrastructure I would be looking at Aruba as a serious competitor. I saw features I’ve not seen yet in other players in the market, the NetEdit software was really interesting and very extensible. They even showed us a mobile app that would allow you to do an initial setup on a new device right from your smart phone using Bluetooth and BLE.
Extreme Networks

The next presenter we heard from was Extreme Networks. The presentation started with an intro from Abby Strong talking a little bit about the company and taking us through Extreme Network’s vision to be a cloud-driven enterprise networking vendor.
We got a demo on their ExtremeCloud IQ showing connected clients, analytics, and event correlation at scale. Gregor Vucajnk took us through Extreme’s use of AI and ML in their Network 360, Client 360, and Device 360. What was really interesting was the impact of the release of the iPhone 11 on their network. They could very clearly see a lot of new 802.11ax (WiFi6) devices show up on their network the day of the iPhone 11 launch.
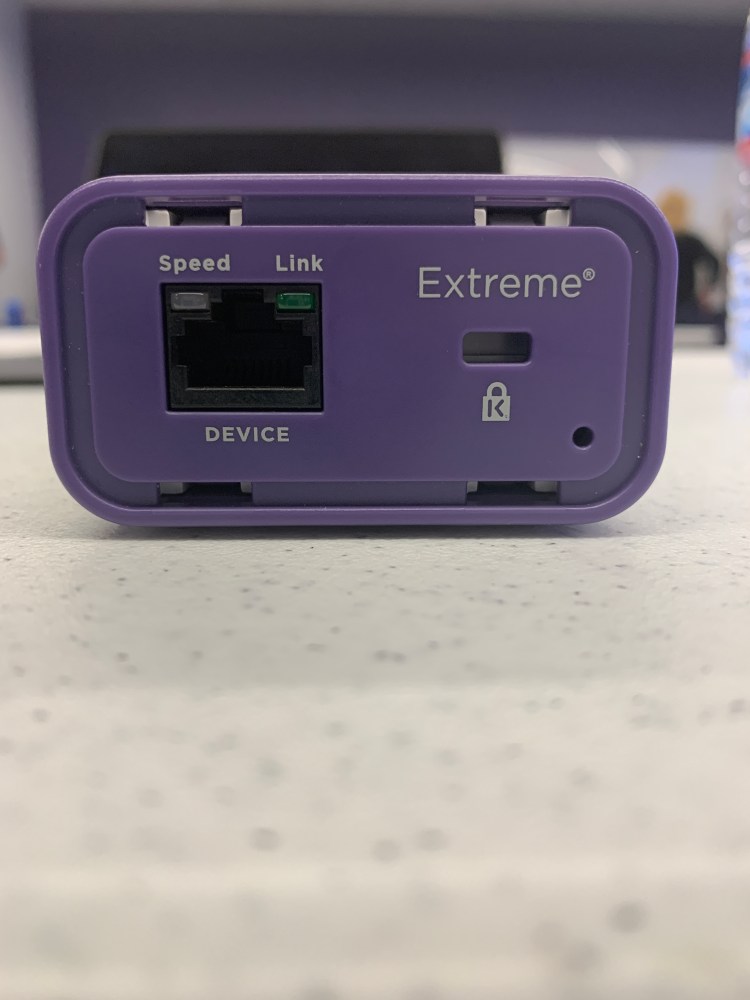
We ended the day with a very interesting presentation and a deep technical dive with Ed Koehler on the complexities driven out of new and emerging threats seen recently, and how that’s driven the near requirement for network segmentation. They also showed us their Extreme defender for IoT.

The IoT defender is like a mini firewall that you put in front your IoT devices. It monitors traffic giving operators visibility into layers 2-7. Even with IoT defender this IoT devices should be kept on a segmented network.
I’ve also got to tell you about the Hackathon that Extreme setup for the delegates. They had an environment running live in the room and delegates volunteered to try and hack the environment. Extreme Networks has hosted this style of hackathon at other events, and even putting a $10K bounty on it. To date no one has been able to hack into it. While the delegates were unsuccessful Kevin Myers gave it a serious run by organizing and collaborating with others in the Network Collective Slack.
IXIA
The last presenter of NFD21 was IXIA. IXIA debuted their IxProbe, a network probe aimed at ISPs to enhance monitoring capabilities .
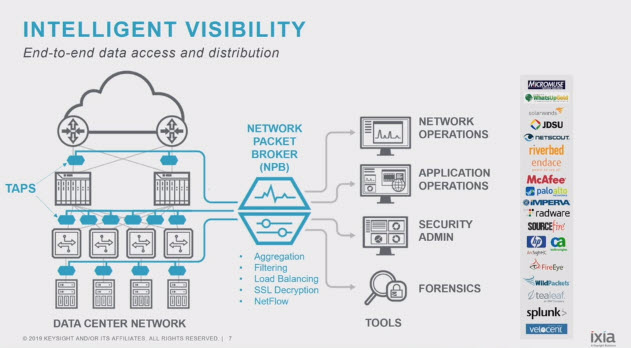
The fully featured IxProbe is installed at the far end of the connection, on customer premise, and is used in part to ensure they are meeting their SLAs, as well as monitor in real-time the overall health of the connection. The probe itself was very small given how feature packed it.

Parting Thoughts
I can’t begin to explain to you how much fun it was to be a Tech Field Day Delegate. If you want to be a delegate I would highly encourage you to apply today! The opportunity to learn from peers in the industry, learn about new technology coming out, hear from networking thought leaders, and see and explore the tech capital of the world was something I won’t soon forget.


One thought